Have you seen this news?
-
Yes. While it’s possible to have encrypted “public” discussions, it makes no sense to me and I don’t know why anyone would do that.
This is exclusively for real private messages (not just “direct” messages)
-
@jaz I agree 100%
It’s too early for anyone to say how Mastodon will design this (even Mastodon)
But this is exactly how I’m doing it in Emissary. Domain owners can choose if they want to support E2EE on their server, and for which groups of users.
Users can also opt in to publishing encryption keys or not.
It’s easy to build this as completely opt-in, so it’s a fair bet that’s how mastodon will architect it.
Make sure they hear your voice as the project gets going in 2027.
>But this is exactly how I’m doing it in Emissary. Domain owners can choose if they want to support E2EE on their server, and for which groups of users.
Tidy, cheers.
-
It’s using “MLS” - a well documented, tested, and tooled protocol.
Private keys are generated on your device (browser, app, whatever). Each device manages its own private keys.
Public keys are posted to your ActivityPub actor profile.
Keys are rotated *very* frequently.. like every time you join a new group.
When someone sends you a message, they address your ActivityPub inbox using a “group key” that includes all of your devices.
Also, we’ve chatted with @soatok abiut this project. They recommended a different management structure, using separate network of key authentication servers.
That’s not off the table, but is more than we can manage right not. It could be another way for us to validate keys in the future.
-
@benpate I'm wondering what the advantage of e2ee private messages on Mastodon is when we have Signal, Matrix and other robust encrypted messaging tools that you could invite a friend to if you want to have a private conversation.
Is anyone worried about this creating moderation issues?
Generally I'm in favor of privacy and security, but I'm just not sure what the value of this feature is on Mastodon. Maybe you or others can provide your perspective on this.
@earth_walker @benpate
Yes.
The very first thing that occurred to me reading this was: "Hmm. Adding E2EE without first implementing the long requested tools to make it less easy to harass people is going to potentially make moderation more challenging and Mastodon more unsafe than it is." -
I would love for that to happen. As soon as I can make a public beta server, you’re all welcome to come and break my code. I’ll pass out treats.
-
@benpate
Ideas for how I explain this to my swaths of very-non-tech friends & family? (Most of whom are happy with FB & Insta & Wassap.)
1. “I left Instagram, so this is how you contact me now…”
2. FB paid a billion dollars for WhatsApp. They wouldn’t do that if they couldn’t use it to profile you. Even if the messages are encrypted.
3. E2EE is being removed from Instagram in a few weeks. Besides, Instagram is creepy and addictive. You can still trade pics on the Fediverse, so…
-
Also, we’ve chatted with @soatok abiut this project. They recommended a different management structure, using separate network of key authentication servers.
That’s not off the table, but is more than we can manage right not. It could be another way for us to validate keys in the future.
@benpate @bluewinds @GroupNebula563 I think you're confused.
The public keys that are rotated frequently are encryption public keys.
The thing I've proposed are for identity public keys.
Using your identity secret key to sign each encryption public key, and having your recipient verify them, is basically a one-liner:
https://github.com/swicg/activitypub-e2ee/issues/35#issuecomment-3738855995
-
@benpate did you hear that Mastodon’s next version implemented Activity Intents, as well? Things keep getting better!
@andypiper @benpate there's no mention (yet?) of this in the ticket (that @benpate opened) at https://github.com/mastodon/mastodon/issues/33984
-
Yes. While it’s possible to have encrypted “public” discussions, it makes no sense to me and I don’t know why anyone would do that.
This is exclusively for real private messages (not just “direct” messages)
@benpate Ok. I don't know how this idea will join the the ActivityPub protocol - or with other words: How all the other platforms in the Fediverse can handle this feature. -
@andypiper @benpate there's no mention (yet?) of this in the ticket (that @benpate opened) at https://github.com/mastodon/mastodon/issues/33984
@adamhotep @benpate thanks for the pointer! We should fix that and link it to the PRs mentioned in Trunk & Tidbits this month…

-
I'm certainly not a lawyer or expert on this, and I'm sure it varies between legal jurisdictions... but I thought that US law has (some?) liability protections for "common carriers" who pass data but are unable to read it.
Your ISP isn't liable for stuff you download over a secure HTTPS/SSL connection. In theory, the same *should* apply here. But still, someone may try to test it in court.
-
@benpate Ok. I don't know how this idea will join the the ActivityPub protocol - or with other words: How all the other platforms in the Fediverse can handle this feature.
It's fully backwards compatible. If you don't support encrypted messages, you can still send/receive regular ones.
Here's a *very* short version:
Your device makes two encryption keys: one is public and one is private
The private key never leaves your device
The public key is published in your ActivityPub profile
If I want to send you a message, I check your profile to see if you've published encryption keys.
Have keys? send encrypted messages
No keys? send plaintext messages -
@benpate @bluewinds @GroupNebula563 I think you're confused.
The public keys that are rotated frequently are encryption public keys.
The thing I've proposed are for identity public keys.
Using your identity secret key to sign each encryption public key, and having your recipient verify them, is basically a one-liner:
https://github.com/swicg/activitypub-e2ee/issues/35#issuecomment-3738855995
Thank you, and yes. Syncing key packages to a public server might get tedious for everyone.
BTW: We had a video conference today, and you came up (along with the issue you linked)
We were running out of time (because W3C meetings) but want to keep open the possibility of implementing this in the future.
We're meeting again in two weeks. Wanna come?
-
I'm certainly not a lawyer or expert on this, and I'm sure it varies between legal jurisdictions... but I thought that US law has (some?) liability protections for "common carriers" who pass data but are unable to read it.
Your ISP isn't liable for stuff you download over a secure HTTPS/SSL connection. In theory, the same *should* apply here. But still, someone may try to test it in court.
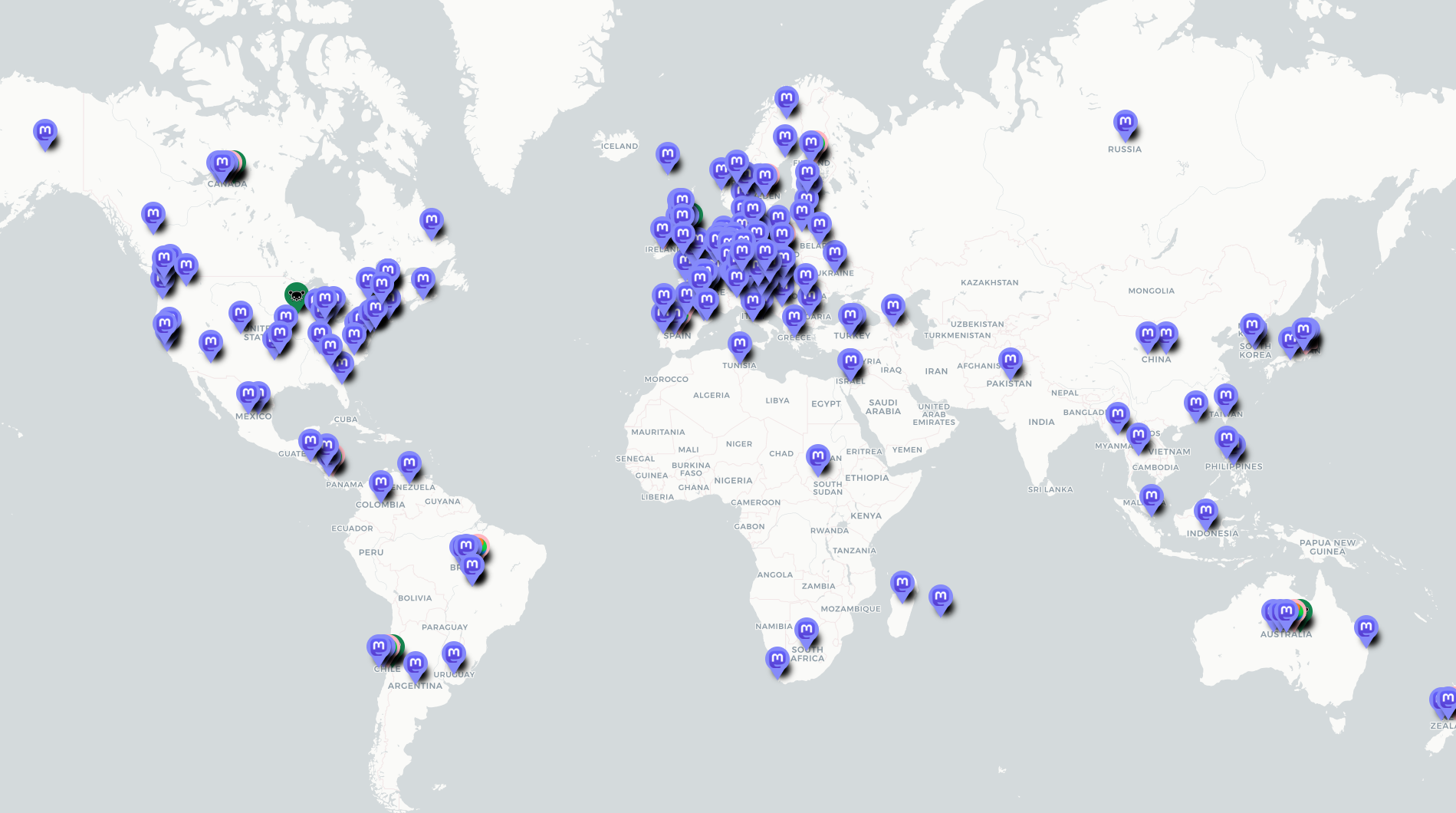
US law is certainly one jurisdiction, one which routinely compels the sharing of metadata of E2EE users and their conversations, and one which is trying very hard to remove a number of protections currently enjoyed by US-based service providers through legislation such as KOSA and EARN-IT.
Also, social media companies are not common carriers. That's a very different thing (like ISPs, telcos, and railroads.)
Also...
https://umap.openstreetmap.fr/en/map/fediverse-near-me_828094#3/25.799891/29.794922
-
@rapsneezy2 Ha! None that I know of

We're (Mastodon, Bonfire, and Emissary) not doing this from scratch. It's building on MLS, which is an open standard for end-to-end encrypted messages that is used by many big players in tech.
Plus, all of this is open source (mine is here: https://github.com/EmissarySocial/conversations-mls) so hopefully any theoretical back doors would be found by interested parties.
If you're interesting in auditing some code, I'd *love* for you to participate!
sadly i'm not qualified to audit cryptogrpahic function enforcing code
but I do recall RSA being open source and being promoted by NIST and the US gov
whilst having known vulnerabilities
https://grahamcluley.com/nsa-bribe-rsa-encryption/
https://www.cnet.com/news/privacy/security-firm-rsa-took-millions-from-nsa-report/
-
-
sadly i'm not qualified to audit cryptogrpahic function enforcing code
but I do recall RSA being open source and being promoted by NIST and the US gov
whilst having known vulnerabilities
https://grahamcluley.com/nsa-bribe-rsa-encryption/
https://www.cnet.com/news/privacy/security-firm-rsa-took-millions-from-nsa-report/
@rapsneezy2 Yup. And, most vulnerabilities have nothing to do with the encryption, but all of the architecture around it that leaks, injects, or lets adversaries circumvent your encryption.
I'm gonna share this image *so many times* today

At the end of the day, I don't think we're building something to keep out the NSA or the Mossad. I think we're thwarting nosy admins, data harvesters, and the same. And that's a good step forward.
Use Signal to do illegal stuff.
-
To be clear, I am very happy E2EE services, patio installers, porn services, and banana peel recyclers exist.
I simply do not want to operate one of these businesses.
-
@jaz I can only say "yes" so many times before I dig up the Meg Ryan gif.
Do you want me to dig up the Meg Ryan gif?
-
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login
